[SWPUCTF 2018]SimplePHP
打开页面,在查找文件处发现任意命令执行漏洞

我们可以通过它来读取文件源码
index.php
1 | <?php |
upload_file.php
1 | <?php |
function.php
1 | <?php |
base.php
1 | <?php |
file.php
1 | <?php |
class.php
1 | <?php |
我们在页面中发现flag在f1ag.php里面,所以我们的目的是读取f1ag.php文件
我们进行代码审计,在class.php中可以看到一个提示
1 | public function __construct($file) |
这个给我们的思路是phar反序列化
入口函数在file.php中
1 | $show = new Show(); |
找到入口函数后,下一步构造pop链
漏洞的利用点在
1 | #class Test |
但这里仅仅是返回了f1ag.php的值,并没有将其打印出来
因此我们还需要一个打印的函数
1 | class C1e4r |
在C1e4r中又打印函数,我们需要利用它,那么思路就很明确了,通过new Cle4r($name),将值传给str,然后自动触发__destruct(),打印test。
说明下一步要考虑name应该传什么
从Test类中我们可以发现,__get($key)=>get($key)=>file_get($value)这样一条利用链,$key的值,是触发__get时传入的$value的值是通过params($key)得到的,所以不妨令params=array(“source”=>“f1ag.php”),然后我们传入$key=“1”,即可
下一步思考怎么触发__get
1 | public function __construct($file) |
令str[‘str’] = new Test(),那么在toString()就是new Test()->source,而source不是Test中的属性,所以就可以触发到get
上面的key之所以为source,是因为这里的new Test()->source调用的就是source不存在属性,这个source被当做参数传了过去
__toString(),反序列化中的魔术方法,当类被当做字符串输出的时候会自动调用toString()方法
令$this->source=new Show()它自身
那么到现在整个pop链条就清晰明了
1 | <?php |
得到生成的phar文件,就要进行文件上传
但由于只能上传gif,jpeg,jpg,png结尾的文件,我们更改后缀再上传
然后访问upload找到我们上传文件得文件名

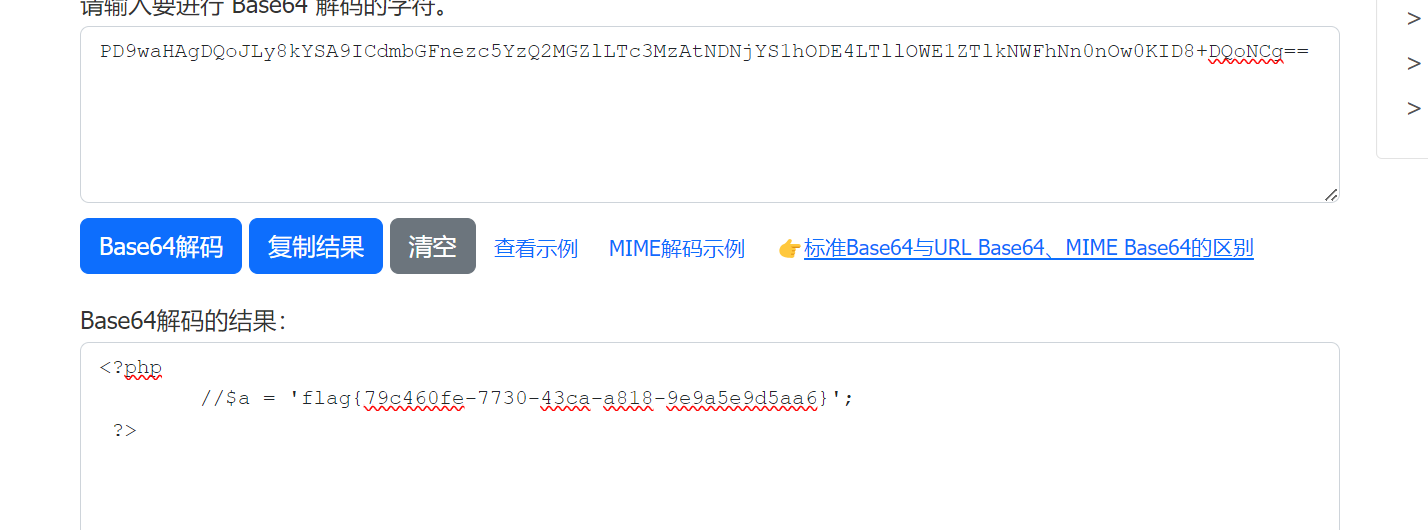
用phar协议访问,得到flag的base64,解码得到flag