[BSidesCF 2019]Sequel
题目没给啥信息,我们来爆破账号密码
爆破后得到账号密码都为guest
登录后,会发现在hacker的那一栏提示我们要以admin的角色登陆,所以本题的大致思路应该就是通过普通用户注入出admin的密码,然后登陆。
我们查看cookie
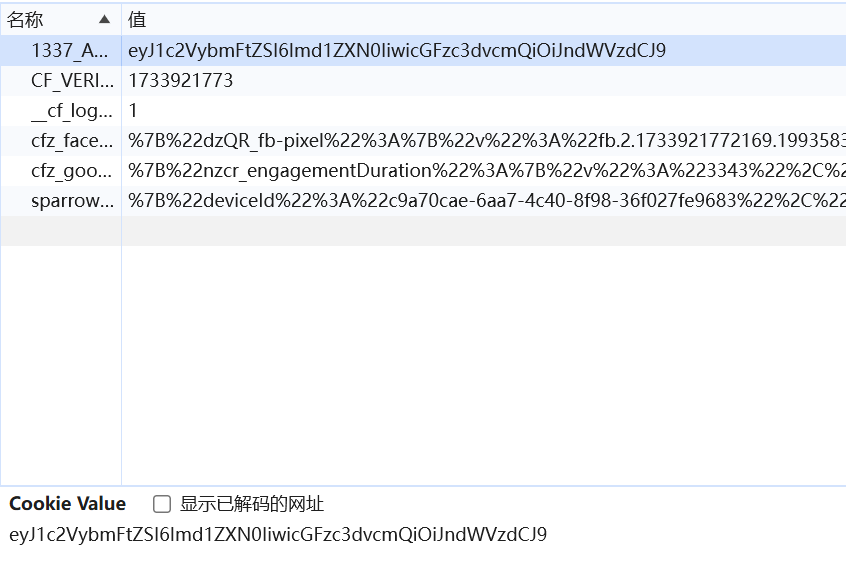
1337_AUTH=eyJ1c2VybmFtZSI6Imd1ZXN0IiwicGFzc3dvcmQiOiJndWVzdCJ9
嗯,长的非常可疑,我们解码看看
base64解码得到{“username”:”guest”,”password”:”guest”}
我们猜测是cookie注入,数据库为SQLite
我们用大佬的脚本
1 | import requests |
查询所有表名(必须自己手工多次查询)
拆了列名 username,password进行查询
1 | import requests |
通过这个脚本可以获得用户名和密码,需要多测试几遍
1 | sequeladmin |
参考